Hardware Cyber Security Assessments for Defence Systems
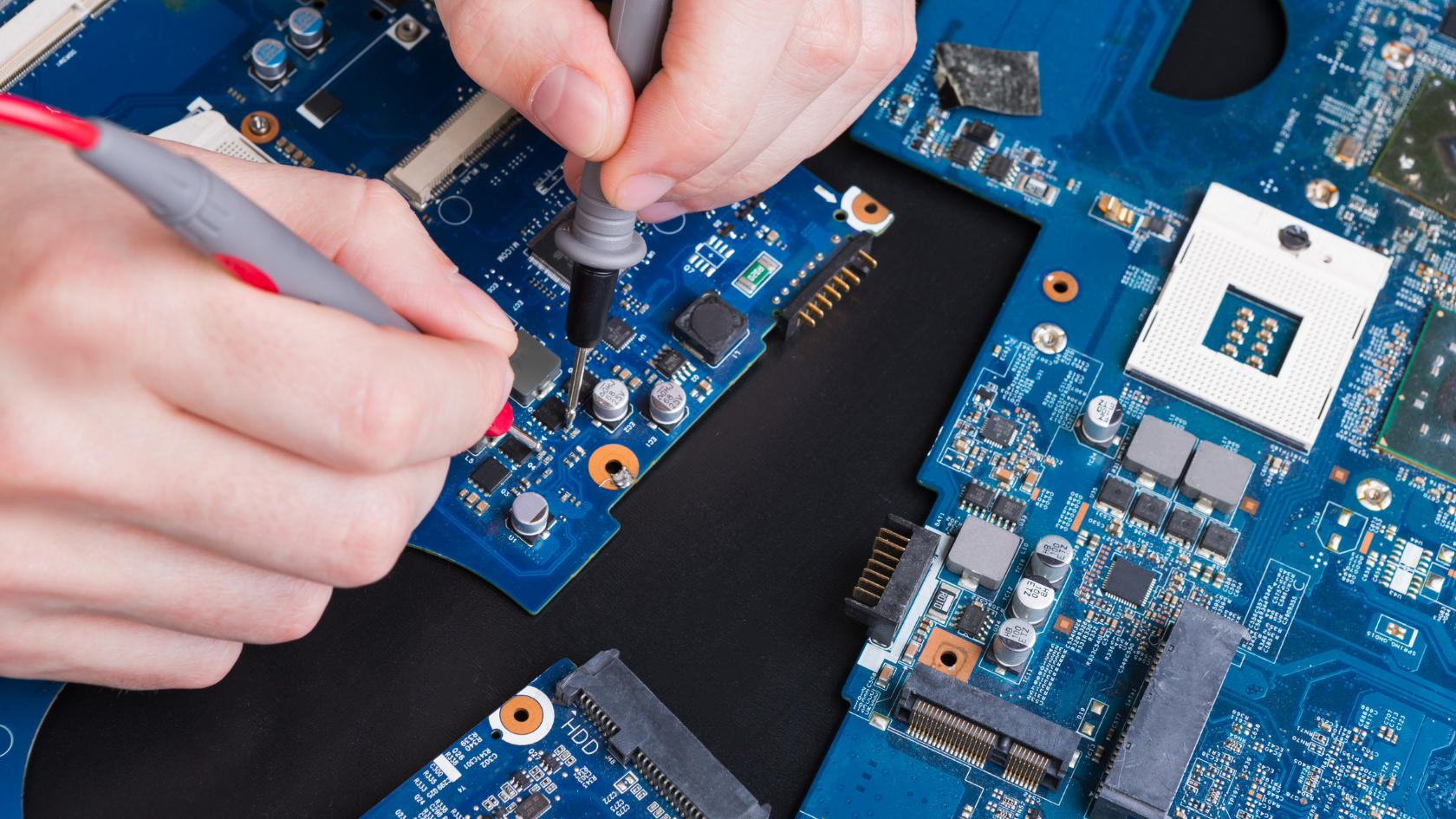
Mission-critical platforms demand trust at the component level. Our hardware cyber security assessments provide that trust by verifying the authenticity, integrity, and cyber resilience of electronic hardware before it enters the Defence environment and throughout its lifecycle. This capability was developed as part of a Defence innovation project for the space ecosystem and has since been used to test military platforms on the ground, protecting sovereign intellectual property and product integrity.
We begin with threat-informed scoping aligned to mission context and classification needs, mapping critical functions, interfaces, and likely attack paths across COTS, MOTS, and bespoke assemblies. From there, we apply a layered methodology that combines design-time analysis with hands-on verification to expose hardware-borne risks early and decisively.
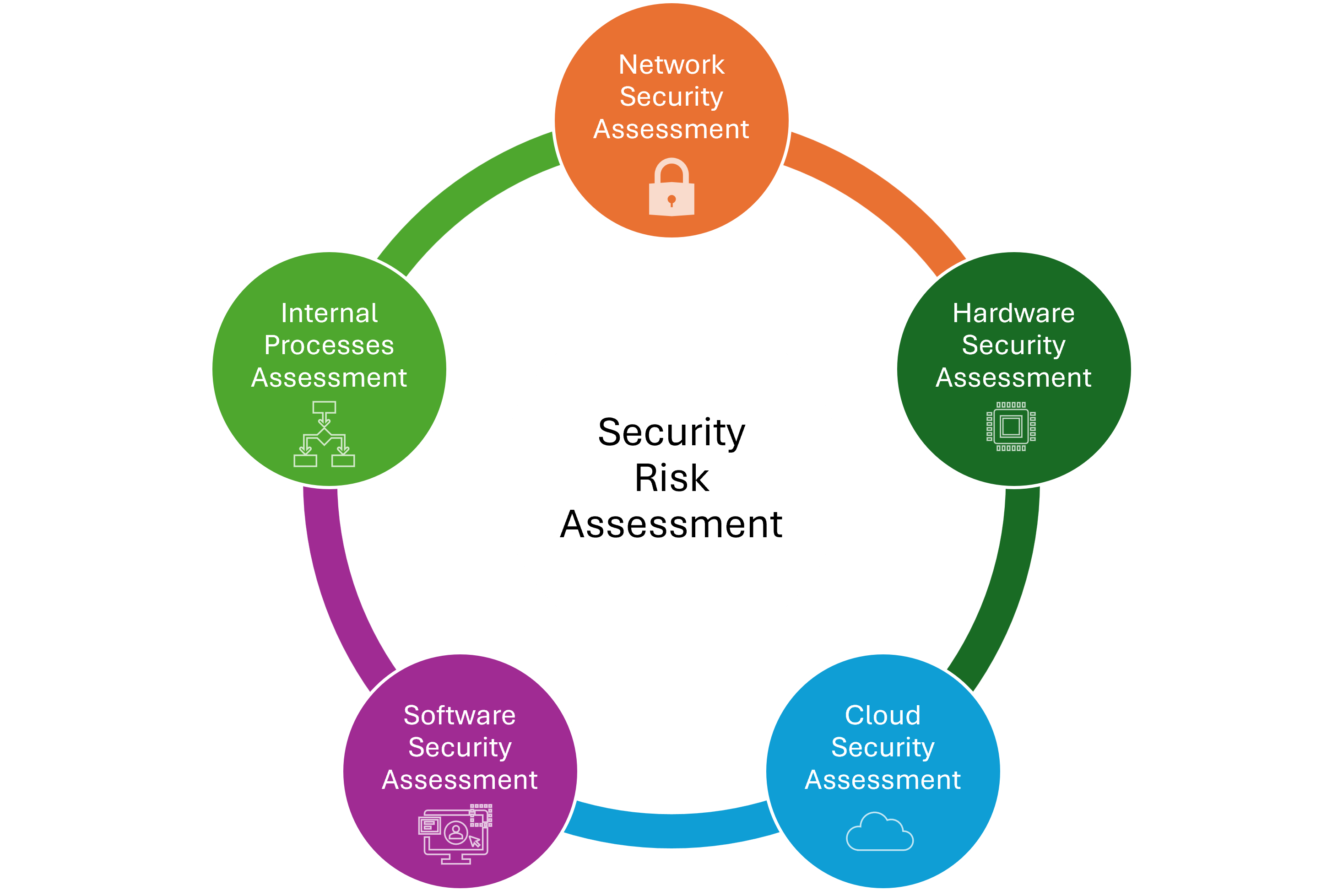
What We Assess
- Authenticity and provenance: Chain-of-custody verification, supplier pedigree, bill-of-materials correlation, and counterfeit detection to prevent compromised parts entering critical systems.
- Firmware and embedded security: Secure boot validation, firmware integrity checks, update mechanism hardening, and configuration assurance to reduce implant and persistence risks.
- Board-level and interface hardening: Review of schematics, debug and test access controls (for example JTAG and SWD), side-channel exposure, and tamper evidence to limit adversary opportunities.
- Supply chain exposure: Component substitution risks, microelectronics trustworthiness indicators, and lifecycle vulnerabilities tied to maintenance, spares, and field support.
- Operational resilience: Fault-injection tolerance, EMI and EMC adjacent cyber vectors, and performance degradations under contested conditions to safeguard mission outcomes.
How We Deliver
- Test planning and execution: Repeatable benches, red-team style probing, and evidence packs traceable to mission requirements and acceptance criteria.
- Assurance artefacts: Clear findings, risk ratings, and remediation guidance packaged for Authorising Officers and integration partners.
- Through-life monitoring: Configuration drift detection, secure update pathways, and re-test on change to keep assurance current across upgrades and sustainment.
Assure Your Hardware. Protect the Mission.
De-risk your next platform, upgrade, or integration with evidence-backed hardware assurance. Contact us to schedule a hardware cyber security readiness review and get a plan tailored to your program milestones and your organisation risk tolerance.